Category: Life technologies
How not to catch the curiosity virus
A person opens the door and sees an envelope lying beneath it with no return address. On the envelope it says: “THIS IS FOR YOU. DO NOT OPEN.”
The envelope will be opened—don’t even doubt it.
Curiosity has always both saved and doomed humanity. It pushed our ancestors out of caves to explore the world. It helped invent the wheel, reach the Moon, and create the internet. And every day, it also makes us vulnerable to those who have learned to exploit this trait.
Over the past twenty years, technology has advanced further than in the previous two thousand: we’ve learned to encrypt data, build security systems, recognize faces and voices. We’ve created blockchain, biometrics, and neural networks. But the human psyche hasn’t changed—it still operates according to rules formed thousands of years ago.
We are still curious about who loves us. We want to see something no one else has seen. We react to urgency (“your account will be blocked in an hour”) and exclusivity (“for you only”). We’re ready to believe almost anything if it promises to make us special.
Curiosity is an evolutionary mechanism that helped humanity survive. But in the 21st century, it needs an update. We’re no longer wondering what’s behind a tree—now the stakes are money, documents, photos, passwords, access to bank accounts, and sometimes even infrastructure that thousands depend on.
We’re not suggesting you stop being curious about the world. We’re suggesting you learn to pause between “I wonder what’s there” and “I shouldn’t do this.”
Let’s take a look at some ways to deal with our own curiosity.
For hundreds of thousands of years, curiosity helped humans survive: something rustles in the bushes—maybe it’s food? Someone left tracks—maybe it’s a mate? A strange noise—maybe it’s danger? Curious individuals gathered more information, navigated the world better, and ultimately survived more often.
Curiosity is a built-in mechanism that pushes us to seek the new—even when we haven’t yet processed the old.
At the core of this mechanism is dopamine. But it doesn’t work quite the way people think. Here, it acts as a hormone of anticipation: when a brain trained over millions of years to respond to novelty senses that it’s about to receive a secret, love, urgent information, something “no one has seen,” it activates before conscious thought does.
That’s why people react to flashy headlines. That’s why they buy the “last item.” That’s why they click links in descriptions. And that’s why they can’t resist finding out what lies behind an intriguing phrase.
Curiosity itself isn’t dangerous. It becomes a problem when something unfamiliar appears—and the anticipation mechanism is already running.
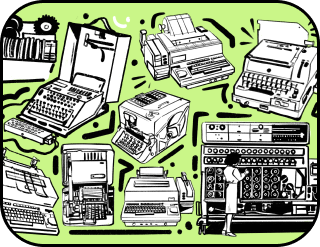
Uncle Simon had a dream. He wanted a miracle in his life. A free one. A big one. Preferably involving money.
And the miracle happened.
One morning he checked his email—and there it was. The subject line burned: “You have won €500,000.” He had never won anything before. Not lotteries, not cards, not even arguments with his wife. And now—half a million euros.
His legs nearly gave out. He opened the email with trembling hands. Everything looked official: logos, stamps, signatures. Some European lottery claimed the draw had been among internet users. Uncle Simon was an internet user. So—it all made sense.
There was just one detail. To receive the money, he had to pay a “processing fee”—only €200. Small change compared to half a million.
He took out his card and began entering the details when… Aunt Hilda walked in.
— Simon, why are you glowing?
— I won! — he breathed, not taking his eyes off the screen.
— A lottery?
Something clicked inside him. Uncle Simon raised his head, looked at Aunt Hilda, then at the screen, then back at Aunt Hilda. His finger hovered over the “Send” button.
One second. He remembered he had never entered any lottery.
Two seconds. He looked at the sender’s address—it was a random string of characters.
Three seconds. He searched for the company’s legal address and found nothing. He moved his hand away from the keyboard.
The email went to the trash. The €200 stayed in his pocket.
And Uncle Simon realized a simple thing: between “I want” and “I did it,” there is a tiny gap—three seconds that separate a miracle from a scam, money from emptiness, laughter from tears.
Now Uncle Simon always counts to three. Even when Aunt Hilda calls him to dinner.
Aunt Mary had a weakness—she loved everything secret and intriguing. So when she received an email titled: “Your husband’s messages leaked. Will open in 24 hours,” her heart skipped a beat.
She knew her husband was a good man—twenty years together, never let her down. But what if? What if there was something? What if her life split into “before” and “after”?
Her finger hovered over the “open” button.
Then she asked herself a question she once read in a smart book: “What will I feel tomorrow morning if I open this today?”
She imagined the morning. Sunlight through the window. Her husband beside her. Coffee waiting in the kitchen. And then—remembering she opened the email. That she read something she couldn’t unknow.
She reasoned it through. If the email was fake, she’d feel foolish. If it wasn’t, she couldn’t verify it anyway—it was anonymous. And most importantly, she would no longer be able to look her husband in the eyes the same way, knowing she doubted him.
Aunt Mary shifted her gaze from the screen to her sleeping husband.
— Oh, forget you, — she said to the invisible sender and sent the email to spam.
In the morning, she woke up, looked at her husband, the sunlight, the cup of coffee he’d left for her by the bed—and thought:
“It’s me who decides what I will think about.”
Sometimes it’s enough to allow yourself to think about something tomorrow.
Uncle George had a habit that annoyed everyone—he asked stupid questions. The most obvious, uncomfortable ones.
When a tiny Telegram channel announced a “new scheme” launching tomorrow and urged everyone to join early, Uncle George just went to drink tea.
— Come on, George, — his friends said. — People are making real money! I’ve seen screenshots!
— And who’s making money off this? — he asked.
— All of us!
— Yeah, right, — he smirked.
His friends fell silent. He finished his tea and went to watch TV.
Now he lives peacefully: no debts, no loans, no stress—because he never figured out “who’s making money here?”
Kevin, Uncle Simon’s distant cousin, had a problem—he thought he knew everything better than others. Kevin could explain how an internal combustion engine works in five minutes, even though he had never opened a car hood. He could tell you why doctors lie about vaccines, despite not remembering the last time he visited a clinic himself. He could invest his last money into a dubious “project of the century” simply because his “gut feeling” told him to.
One day he got a call. A pleasant female voice said his bank account had been hacked, and his money was about to be stolen. He urgently needed to transfer everything to a “secure account.”
— Is all your money on the card?
— Yes.
— Then let’s hurry, I’ll dictate the payment details.
He took out his card. And suddenly remembered his old teacher, Mrs Molly—a kind elderly woman who always smelled like pies.
In his mind, he asked her: “Should I transfer it?”
— Kevin, — she said quietly in his imagination, — are you sure this is the bank?
Kevin froze. Then he hung up. He went to the bank’s website, found the support number, and called. Five minutes later, it turned out that his money was perfectly safe, there had been no hack, and the “secure account” was actually a scammer’s wallet.
Kevin sat there, staring at his phone. For a moment, it seemed to him that he caught a faint smell of freshly baked pies.
Since then, before doing anything important and urgent, Kevin always imagines someone he trusts standing next to him. Sometimes it’s Mrs Molly, sometimes Uncle Tom the physicist, and sometimes just some smart guy from the Internet.
When curiosity switches on automatically—without questions, without a pause—you become easy to manipulate. All it takes is a promise of a secret, love, something free, or a forbidden fruit. And suddenly you want to open, click, buy, believe.
But curiosity can be made conscious.
Three seconds of pause. A question about tomorrow morning. A thought about who profits from this. The imagined look of a trusted advisor.
Each of these techniques is simply a way to remind yourself: I am in charge here. Not emotion, not dopamine, not intrigue—me.
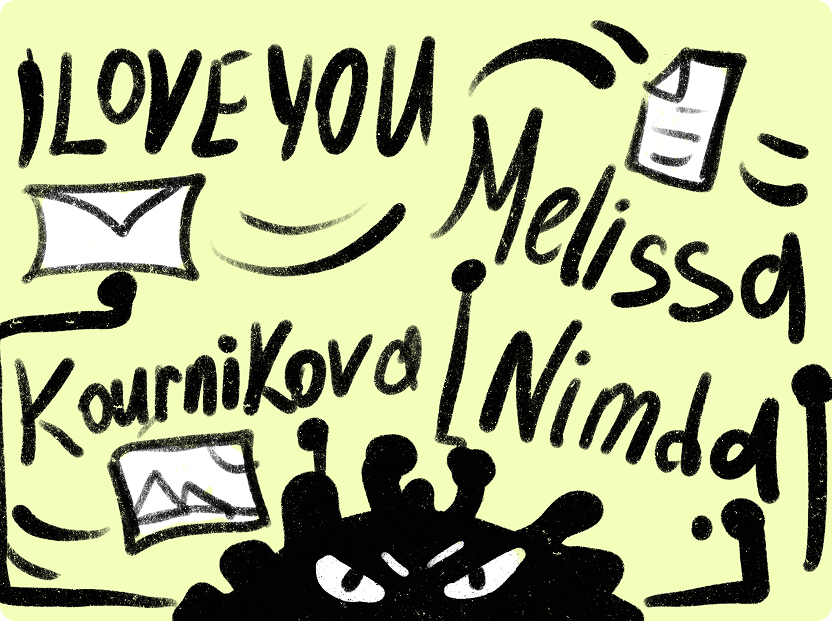
Curiosity isn’t just dangerous in everyday life—it can take down entire industries. Over the past twenty years, scammers have learned to exploit human curiosity better than psychologists, and the history of famous computer viruses proves it.
Familiar + unknown = curiosity
ILOVEYOU. May 2000. Morning. Coffee. Laptop. Herbert checks his email—there’s a message titled “I LOVE YOU.” The sender is his friend Jed. “And why on earth would my buddy suddenly start sending me emails like this? Even if he had strong feelings for me—or something worse—why would he want to bring that kind of truth into my sunny world?” Herbert thought. But he opened the email anyway. Inside was a text file—indeed, a love confession.
The file was called LOVE-LETTER-FOR-YOU.TXT.vbs. But at the time, Windows hid file extensions by default, so Herbert—and everyone else who received the message—only saw LOVE-LETTER-FOR-YOU.TXT. What could be safer than a text document?
In reality, everyone who received that email got one of the most widespread viruses in history. Once opened, the virus sprang into action: it copied itself into the system folder under two names—MSKernel32.vbs and Win32DLL.vbs—then added itself to the system registry to run every time the computer started. It accessed the Outlook address book and sent itself to all contacts. In the “sender” field, it used the previous victim’s address, so the email appeared to come from someone trustworthy.
Then the virus began scanning the computer’s drives—looking for photos, music, documents. Whatever it found, it replaced with its own copies, permanently destroying the originals. Vacation photos, a thesis written over sleepless months, music, files, movies—everything was reduced to nothing. After that, the virus downloaded a trojan from the internet that stole passwords and sent them to its creator.
The author of the virus was a Filipino student named Onel de Guzman. He studied at a computer college and struggled with the high cost of internet access—providers charged significant fees for traffic. As his thesis project, he proposed creating a program that would steal access passwords so that “everyone could use the internet for free.” The review board rejected the idea.
So he dropped out and wrote the virus anyway. At first, he limited its spread to the Philippines, but then—out of curiosity—he removed the restriction. The virus spread worldwide and, within weeks, infected 55 million computers.
The Pentagon went down. The British Parliament went down. Even the CIA let the virus into its systems. Major companies shut down their email servers to stop the flood. U.S. mail systems alone spent $20 million on cleanup. The total damage reached $15 billion. The virus, with its romantic name, entered the Guinness World Records as the most destructive in history.
Police quickly tracked down the student—floppy disks with the code were found in his apartment. But at the time, there were no laws in the Philippines against creating malicious software. Today, Onel de Guzman runs a small phone repair shop and says creating the virus was a mistake—he never expected it to spread so far.
ILOVEYOU demonstrated a simple truth: the most reliable way to infect a computer is to impersonate a friend.
When a message comes from someone familiar, the brain automatically lowers its guard—and curiosity activates before caution has a chance.
Forbidden + free = curiosity
Melissa. March 26, 1999. Some user in New Jersey posted a file called list.doc in the “alt.sex” newsgroup—a regular Word document that supposedly contained passwords to 80 paid porn sites. Who would say no to free porn? No one did.
Users began opening the file en masse—and nothing happened. Of course, there were no passwords inside. Instead, the document contained a macro—a small Visual Basic program that ran automatically when the file was opened.
The macro did two things: it accessed the Outlook address book and sent itself to the first 50 contacts. The email arrived with the subject “Important Message From (sender’s name)” and the message: “Here’s that document you asked for… don’t show anyone” and a winking smiley at the end.
Then the virus embedded itself into the Normal.dot template—the file where Word stores default settings. After that, every new document created by the user automatically became infected.
There was even an easter egg: if the current minute matched a certain number, the virus inserted a quote from The Simpsons into open documents: “Twenty-two points, plus triple word score, plus 50 points for using all my letters. Game’s over. I’m outta here.”
The creator of the virus was David L. Smith. At the time, he worked as a programmer in New Jersey and, apparently, was bored. During questioning, he admitted naming the virus after a stripper from Florida he once met. He created it out of curiosity—to see whether he could build something impactful.
Within days, Melissa infected over 100,000 computers—no one knows the exact number, because it spread too fast to count. Mail servers at Microsoft, Intel, and Lockheed Martin went down almost immediately. The virus even disrupted the Pentagon and the U.S. Marine Corps. Total damage was estimated at $80 million.
Smith was caught quickly—the FBI traced him within four days. The code contained digital fingerprints—GUIDs—that led straight to him. In court, he pleaded guilty, cooperated with investigators, and received 20 months in prison and a $5,000 fine. Later, he even worked with the FBI, helping catch other cybercriminals.
Melissa exploited one of the oldest hooks in human psychology—the forbidden fruit. When people are promised access to something usually hidden—compromising information, passwords, private messages—curiosity almost always beats common sense.
Useless + but interesting = curiosity
Kournikova. February 11, 2001. “Want to see a nude photo of a tennis star?” Millions of people received an email with the subject: “Here you have, ;0)” and an attachment named AnnaKournikova.jpg.vbs.
Recipients didn’t really know why someone would send them a photo of Anna Kournikova—but they opened it anyway.
Of course, the file showed no photo. Instead, it launched a virus—a simple Visual Basic script. It didn’t destroy files or corrupt data. It just spread—quickly and relentlessly.
Later it turned out the virus had been assembled in just a few hours using a ready-made tool called [K]Alamar’s Vbs Worm Generator—a program where you simply choose settings (name, spread method, email text) and click “create.”
The author was a 20-year-old Dutch student named Jan de Wit from the town of Sneek. He was browsing the internet and came across an article claiming that people hadn’t learned anything from the ILOVEYOU virus. That made him curious: would anyone really fall for such a simple trick again?
He downloaded the generator, clicked a few buttons, created the virus, and released it into an online forum around 3 p.m.
Later, he told the police he didn’t know how to program, didn’t mean harm, and simply liked Anna Kournikova—“she deserves attention, doesn’t she?” He also added: “Those who opened the file are to blame themselves.”
Within hours, the virus spread worldwide, infecting hundreds of thousands of computers. The damage was estimated at $166,000.
After talking with his parents, de Wit decided to turn himself in rather than wait to be caught. He walked into a police station three days later.
Interestingly, the mayor of Sneek wasn’t outraged. He offered de Wit a job in the city’s IT department—arguing that the town should be proud of such a talented young man.
The student was tried in Leeuwarden. The prosecutor asked for four years in prison and a $40,000 fine, but the court took into account that the virus didn’t damage data and sentenced him to 150 hours of community service.
The Kournikova virus was primitive—but perfectly calculated.Sometimes curiosity isn’t about discovering the truth. It’s about the urge to check for yourself.
Hole + inaction = curiosity
Nimda. September 2001. America had not yet recovered from the attacks when a new blow struck — a virus called Nimda. Read the word backward—it becomes admin, or the one who has full access to everything.
Nimda was an infection machine with five ways to penetrate your computer. Five.
The virus sent itself to all addresses it found in the address book. The emails contained a file named README.EXE. But the cleverest part was that you didn’t even need to open the attachment—just opening the email in Outlook would let the virus enter your computer, exploiting a vulnerability in Internet Explorer related to improper MIME-type handling.
If your computer had shared folders open, Nimda would find them across the network and copy itself there. All it took was someone opening such a folder, and the virus would jump to the neighboring machine.
Nimda scanned the Internet for servers with IIS vulnerabilities, found them, and copied itself onto the server.
The virus modified all HTML pages it encountered on a server, embedding a snippet of JavaScript. Anyone visiting such a site automatically downloaded the virus, and if the user had an older browser—it would execute automatically.
Nimda also exploited loopholes left by other viruses—Code Red II and sadmind. That is, if your server had been previously compromised, Nimda would arrive and claim it for itself.
Interestingly, the author of Nimda has never been found.
The virus was released on September 18, 2001, a week after the planes hit the World Trade Center towers. Some media immediately suggested ties to Al-Qaeda and cyberterrorism, but these theories quickly dissipated, as no connection was found.
There were strings in Nimda’s code pointing to China. But this could have been a false lead—such things can be faked. In Canada, for example, on October 11, 2001, someone sent emails supposedly from Mikko Hypponen, chief antivirus expert at F-Secure. Inside that email was Nimda. So the virus author(s) could have been anywhere. The only person caught from that era was the one who wrote a version of Blaster. Nimda, however, remained a ghost.
Nimda spread at a furious pace: in 22 minutes it infected hundreds of thousands of computers. Estimates of the damage reached $2.6 billion. The virus didn’t destroy files; it replicated itself thousands of times. On an infected machine, every folder could contain dozens of .eml and .nws files. Some Microsoft employees even called Nimda’s creators “industrial terrorists.”With Nimda, curiosity worked in reverse: “What happens if we do nothing?” Maybe the author was a genius. Or maybe they simply knew people are prone to leave the door open, just to see who knocks.
Freebie + hope = curiosity
CIH. April 26, 1999, saw a global pandemic in the computer world like no other. The CIH virus affected over half a million computers worldwide, destroying all data on their hard drives.
This virus was remarkable because it would reliably trigger on April 26th each year (hence its nickname Chernobyl) and because a single infection could, quite literally, physically destroy any computer. As a result, data on hard drives was erased, and the contents of BIOS chips on motherboards — the tiny programs that instruct the device on how to start up — were damaged. The CIH virus simply overwrote the BIOS.
In the late ’90s, the Internet was expensive and slow, so people often shared disks. You could buy a cracked Half-Life or Quake II disk, or download a long-awaited game from an FTP server, already containing the infected setup.exe file. Launching the setup instantly loaded the virus into memory, infecting all EXE files commonly used: browsers, calculators, Winamp, even Half-Life itself.
How did it work? The virus looked for gaps in files — like finding space for a new chair in a fully furnished apartment. Usually, between the end of one section and the start of the next, there were unused bytes; the virus inserted its code there. File sizes remained unchanged, just as your apartment’s square footage doesn’t increase with a new chair. If no gap existed, the virus split its code into blocks and appended them to various sections of the file.
Once a file was modified, the virus checked the system date and began sequentially destroying data and BIOS.
By accessing the disk directly, it bypassed built-in BIOS protection. When CIH triggered, users saw only a black screen on startup. Nothing else.
The only remedy was replacing the motherboard and reflashing the BIOS. Recovery utilities often failed.
Initially, the virus spread through local internet forums, escaping Taiwan within a week to infect computers in other countries. About a month later, it appeared on American gaming servers, likely causing the epidemic — users downloaded games, unwittingly receiving CIH.
The virus was created by a student at Taiwan University — Chen Ing-Hau. He was studying engineering, writing small computer programs, and experimenting with viruses for educational purposes. Later, he bought an expensive, powerful, high-end antivirus, only to find that it didn’t protect him or his computer’s data at all.
Chen got angry: he had paid money and received a useless program that didn’t work. So he decided to punish the manufacturers and prove that all antivirus software was, in his words, “absolute garbage.” After the virus began spreading uncontrollably and accumulating many modifications, Chen wrote and publicly released a utility that could detect and remove the virus, which helped him avoid jail time in 1999. However, in 2000, he was still convicted, and in many countries Chen Ing-Hau remains a persona non grata, considered a dangerous hacker.
CIH is a perfect example of curiosity, even though it didn’t spread through emails or enticing headlines. The virus relied on a different type of curiosity — the desire to bypass rules. In the late 1990s, games were expensive, the internet was slow, and there was a disk on the market:
“Half-Life — full version + crack + trainers.”
A person feels like a bit of a hacker because they’ve found a shortcut: “maybe I can get it for free?”
Knowledge + ignorance = curiosity
Curiosity cannot be cured. And that’s a good thing. Thanks to curiosity, humanity traveled from the Stone Age all the way to neural networks.
The problem is that over the past twenty years, far too many people have wanted to ride this engine of progress. Curiosity arises every time there is a gap between what a person knows and what they could know.
But there is good news: curiosity can be made conscious. It won’t stop being curiosity; it will just stop being automatic. In this article, we’ve outlined ways to become friends with it. You will still want to see what’s behind the door, only now you’ll check where that door actually leads.
Technology changes, scammers become more convincing, and humans remain human. Curiosity survived in the caves and now actively consumes the internet. Don’t stop being amazed — learn to think fast enough to keep up.
A navigator determines the current location of a person on Earth. We’re mapping new routes in your consciousness.
Thank you!